The Security tab is used to configure a
node's security feature. The security feature applies
policy-based resource access with roles.
A user is paired with a role, a role is given access to
resources in a policy, and multiple priority based policies
can be defined and enabled.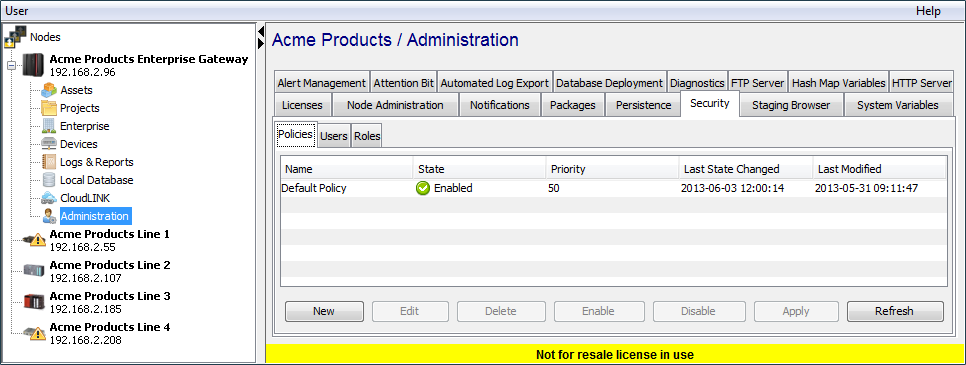
User name and password when using the Workbench Log on window
The Workbench itself does not have a concept of
a user logging on before being authorized to access
features in the Workbench.
Rather the Workbench uses the user name and
password supplied when connecting to each and every
node. The user names, passwords and access control
configuration is a feature of each node.
This allows flexibility, if needed, in defining
separate access control configurations for each
node.
Security summary
- The security feature is a feature of each node, where the access control information is configured. The Workbench passes the user name and password used to Log on to the Workbench to the node for authentication and authorization.
- The User logged on to the Workbench is recorded in the activity messages written to the Audit Log.
- The security feature is used to define Users, who have one or more Roles.
- Roles are given access (allowable actions, such as: view, read, write, execute, delete, etc.) to resources. This is done in a Policy.
- Multiple Policies can be enabled at one time.
- Policies have a Priority, which is used to apply precedence to determine a Role's access to a resource.
The sequence of updating or defining new Users, Roles and Policies will depend on whether the node already has definitions that will be updated and added to, or whether new definitions need to be made.
For example:
- If the current definitions of Roles and Policies are adequate, then a new User can be added and assigned a Role.
- If a new Role is required for the specific actions allowed for resources, then a new Role would be first be defined. Existing or new Policies would then be updated or defined giving the Role the specific actions allowed for resources. Users can be updated or added to have the specific Role.
- Policies can be Enabled or Disabled. Multiple policies can be enabled. The policies' priorities are used to apply precedence to determine a Role's access to a resource.