The device manager component and the device drivers
support the ability to set up security access down to the
individual device variables.
This is referred to in the Device connectivity
and individual device driver sections as Per Variable
Security.
For some products, the default setting when defining devices for Per Variable Security is False. For other products the default is True. The considerations when deciding to use this ability include the following:
- Use of this ability for a device definition will mean more system memory is used, since control structures are required to track the device's variables and whether each role has read or write access to each variable. This can be a significant amount of overhead for products that run on systems with limited memory resources.
- Not using system memory for Per variable Security for devices where it is not requirement will mean more system memory is available for other portions of the application, including: more started devices, more executing triggers, etc.
- The requirement to control access down to the variable level versus just to the device level.
- The requirement to control access at the device level versus the trigger level.
At any time, you can define a device to use per variable security and define the security policies required to grant the desired read and write access to roles and users down to those devices' individual variables. This is completely based on the application solution's requirements and the ability of the application to execute properly in its system environment, including the availability and use of system resources such as CPU cycles and memory.
You will know that per device variable security is not
enabled for a device, because the device will not list its
variables under the Read and
Write actions. For example: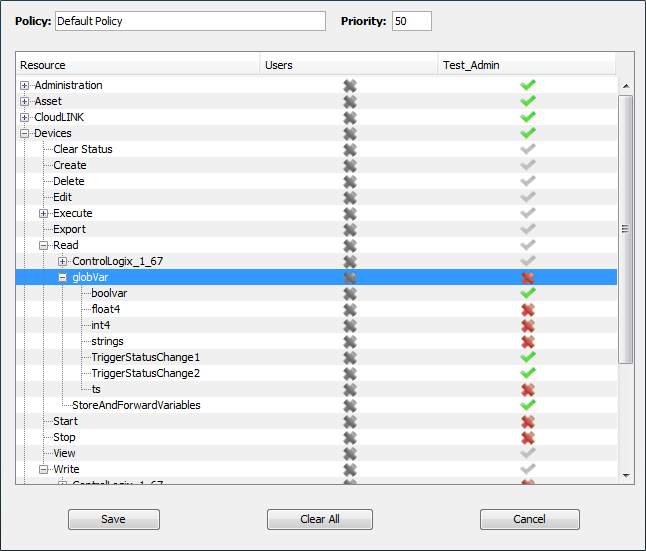
This example shows a portion of the Policy window and the policy named Default Policy. The devices ControlLogix_1_67 and globVar list their variables, as seen by the [+] or [-] icons and the variables names. These two devices must have Per Variable Security defined to True. The device StoreAndForwardVariables is not listing its variables, so it must have Per Variable Security defined to False.
If per variable security is not defined to True for a device, then the access control is limited to granting Read and or Write access to the device as a whole, and all of its variables. This may be sufficient for some applications.
If per variable security is required, then the following
steps will enable and verify this level of access
control:
- Edit a device's definition to have Per
Variable Security set to
True. This parameter may be controlled
by a Use Advanced Properties
checkbox.

As part of editing a device, you may need to complete the edit and then Start the device. - Edit the appropriate security policy to grant or
deny Read and Write access to each of the device's
variables.
In the example Default Policy above, the Test_Admin role has been granted Read access for the globVar device's boolvar, TriggerStatusChange1, and TriggerStatusChange2 variables. Read access has been denied for the remaining variables.
Define or update the users that will have the variable access defined for the role used for the policy. Enable the policy that contains the defined variable access. - Verify each user's access to the devices and the
device variables defined in the policy.
This can be done by temporarily logging on as a user with the Use Alternate Credentials option, then using the Variables window to display, read and write each of the variables.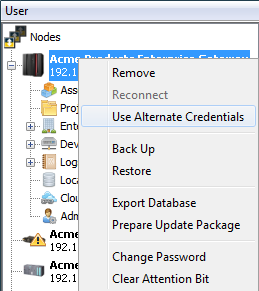
If the user does not have Read (or Write) access, an appropriate error message is displayed. For example: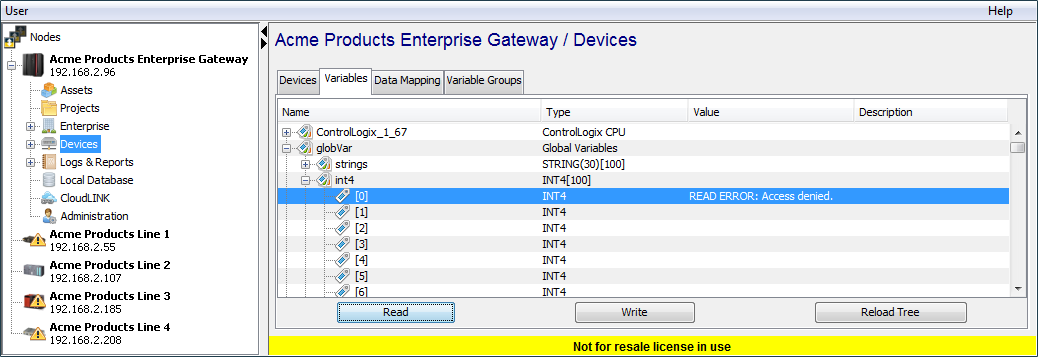
After you have verified the proper read and write access
has been enable for the user, the application development
and verification can continue.